
Internet Security Training
- Prevent and avoid yourself from becoming a victim of cyber attacks
- Detects and report any suspicious activity
- Learn the operations of cyber crime
- Controls data from being accessed and stolen by others
- Reduces damage and loss if your device is attacked
- Training Delivery
Hands-on Classroom Workshop
- 2 Days
- Fundamental
- Difficulty Level
- Pre-requisites
Suitable for all
- Register Now
Training Overview
Internet Security Training is a training designed to provide awareness and guidance to internet users on how to prevent and prevent themselves from becoming victims of cyberattacks.
Throughout the training, participants will be introduced to various tactics and modes of operation of cyber attacks and ways of detecting cyber attacks. Participants will also be taught how to set a strong personal account password and improve security by using security software such as Google Authenticator. And participants will also be given guidance on how to handle the situation if attacked.
At the end of this training, participants will learn how to track any activity involving suspicious internet use. In addition, users will also be able to use a strong password for their account, and control data from cyber attacks, while reducing the risk of damage and loss.
A simple ransomware could ruin your company business

Ransomware is a malware that encrypts a user’s files and demands cryptocurrency in ransom to unlock them and spread across the world in a coordinated cyberattack.
How ransomware happen:
1

A warning popup from WannaCry appear that files are encrypted
WannaCry searches for and encrypts 176 different file types and appends
2

Victims were instructed to send ransom payments
It asks users to pay a US$300 ransom in bitcoins.
3

Payment amount will be doubled after three days
The ransom note indicates that the payment amount will be doubled after three days.
4

If payment is not made, encrypted files will be deleted
If payment is not made after seven days it claims the encrypted files will be deleted.
See for Real
#Smominru botnet, which uses the same vulnerability as #WannaCry and #NotPetya is infecting over 4,000 PCs EVERYDAY. https://t.co/OFP6xNRy4Q
— Kaspersky (@kaspersky) October 20, 2019
56% of utilities faced a cyberattack in the last year
— BitDam (@BitDamSecurity) October 17, 2019
25% affected by WannaCry or NotPetya#WannaCry #NotPetya #malware #cyberattackshttps://t.co/1ai2A5m92M
#WannaCry is still spreading, so why don't we hear about it? https://t.co/ZEzK7YQv9f @BrianKrebs: is this a sleeping WannaCry timeBomb?
— Micha A. Hugelshofer (@MAHugelshofer) October 15, 2019
TWiT Bits #Podcast Episode about #RansomWare with broken payload. #CyberWar #CyberSecurity #KillSwitch
/cc @vecirex
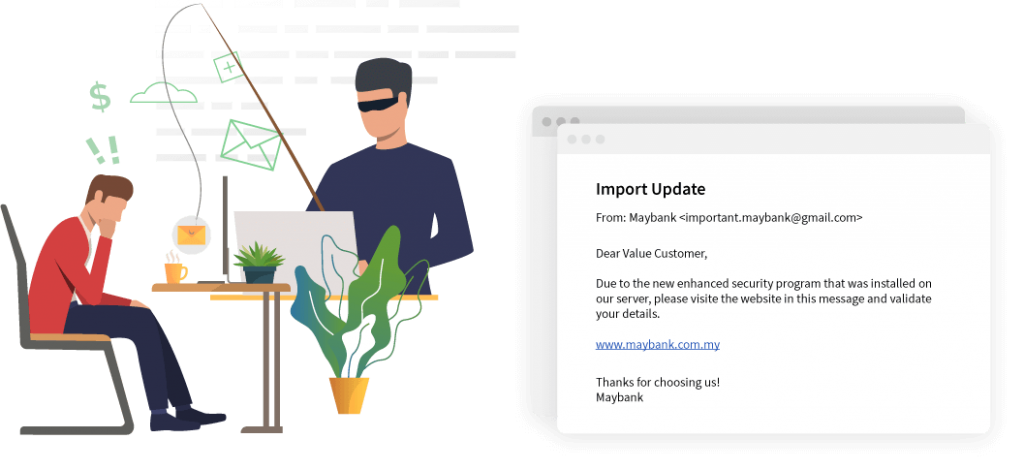
Phishing Attack Prevention
The majority of emails are opened on mobile devices, scammers have ample opportunity for a successful phishing attack. Hence, our internet security training will guide you on how to identify & prevent phishing email.
Do you know that a hacker can monitor you from your webcam & microphone?
Learn how to secure your webcam and microphone from hackers

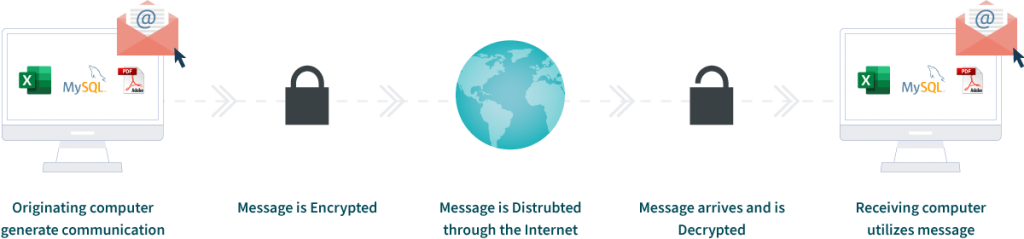
Email encryption flaw and keyloggers allow hackers target easily on full access to your secret messages


Backup your data on cloud and protect your data
If you are using a computer or mobile device for long enough, something will go wrong sooner or later, can causing you to lose your personal files, documents or images.
For instances, you can accidentally delete your files, have a hardware malfunction, lose a device or get infected with malware such as ransomeware. Backups often are the only way to rebuild your digital life in the moments like these.
Why you should attend this Internet Security Training?
Reduce Errors
Learn about common scams, such as email attachments that contain malware or phishing emails that steal personal information.
Enhances Security
Use strong passwords, flag suspicious emails, and alert supervisors about unusual communications or activity
Protect Company’s Reputation
A breach of security can ruin the brand's credibility, causing customers to flee in droves.
Helps Morale
Educate everyone discreetly, enhancing job satisfaction and employee retention along the way.
Save Time and Money
Save the time from identifying and recovering from cyber-attack. And save the cost of typical disruption to business operations, upgrades or replacements.
Peace of Mind
Having a strong security policy coupled with security awareness training means less worrying.
Training Outcomes
At the end of this Internet Security Training, participants will be able to:
- Flag suspicious emails and alerting supervisors about unusual communications or activity
- Prevent cybercrime
- Mitigate data and security breaches on time to minimize the dangers
- Behave in a socially responsible manner
- Prevent breaches and attacks
Who should attend the Internet Security Training?
This is a non-technical Internet Security Training which is suitable for everyone who uses the internet.
Employers
Employees
Students
Government Staffs
Home Users
For anyone who use a computer with Internet connection.
For anyone who wants to learn more about internet security and privacy.

Why Choose Our Internet Security Training?
Since operating in 2008, we have conducted over 400 course sessions and trained over 10,000 participants. Our courses have also received HRDF recognition and approval.
What You Will Get?

Hands-on Learning, Taught by Expert
High-quality classrooms that utilize hands-on learning training, intentional spaces, provided with computer and WiFi.

Personalised Mentorship
Get a knowledgeable mentor who guides your learning and is focused on answering your questions, motivating you and keeping you on track.

Continue to Learn with Online Learning
1 Year Access to LMS with step by step videos & guidebook exclusively produced by MU DOT MY PLT.

After Training Support
Get 3 months free email support after your training. Email to our trainer anytime.
Read more

Certificate of Completion Provided
Participants will receive a Certificate of Completion on the last day of training.
Follow Up Training
Every participant entitles for 1 free follow up training. Follow up training will be scheduled in the future. This will help you to catch up your learning.
Read more
Bonus in Training
We provide a checklist of best practices precaution measures for FREE!
Register Now / Get A Quote Now / Request Brochure
In-Person/Virtual Training
Clients can attend the in-person training at our computer lab or join the virtual training. Pay per person.
In-House Training
Conduct this training at your office anytime, anywhere. Maximum attendance of 25 pax. Just pay per day!

MOF No: 357-02240271
